CrowdStrike Fusion Workflows
A collection of CrowdStrike Fusion (SOAR) Workflows
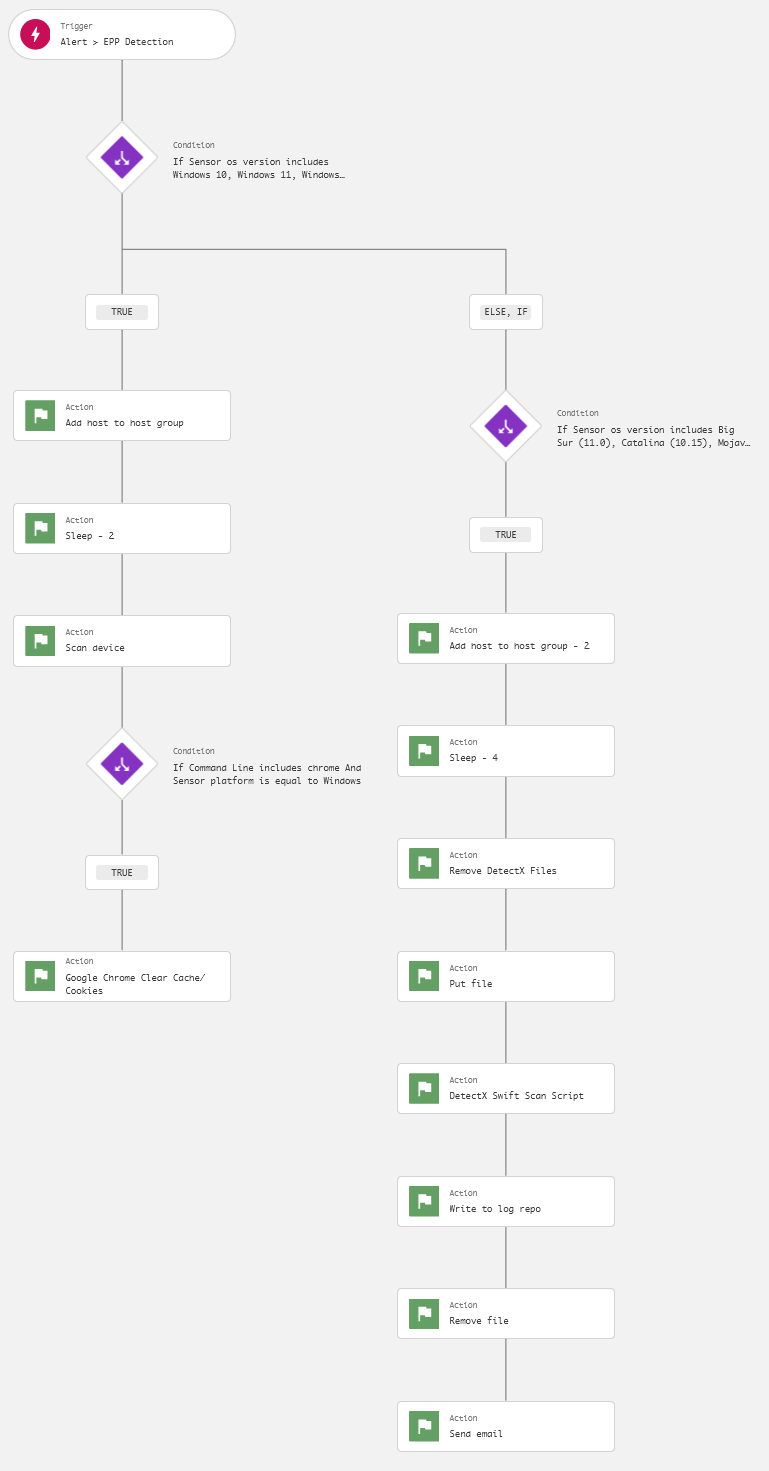
EPP Automated Malware Scanning
For both Windows and macOS EPP high/critical severity detections, the host is added to a hostgroup with a response policy enabling Real-Time Response custom scripting. The process is not instantaneous, so we allot 3 minutes for the operation, setting the workflow to sleep.
On Windows, on-demand scan is initiated with “aggressive” detection and prevention levels for on-sensor and cloud antimalware capabilities, and a CPU utilization limit of 1%. This balances the requirement for automated malware response with minimal performance degradation. If the process which triggered the detection is Google Chrome or Chromium, a PowerShell script which clears browser cookies and cache is invoked.
On macOS, a zsh script clearing “DetectX” files is invoked before a new DetectX Swift application ZIP file is placed in the /private/tmp directory. Another zsh script is executed to extract the ZIP file and initiate a full command-line scan and output the results to /private/tmp/detect.txt. The original ZIP file and extract files/folders are removed once the scan is completed. The results of the scan are written to LogScale under a custom field name and an email is sent to targeted recipient informing them of a completed scan for a given host. The analyst can examine the scan output and initiate a Real-Time Response session with the host to remediate findings.